Unlocking AI Security: Nvidia Rubin’s Rack-Scale Encryption Blueprint
Cryptographic Trust: The New Frontier in AI Security
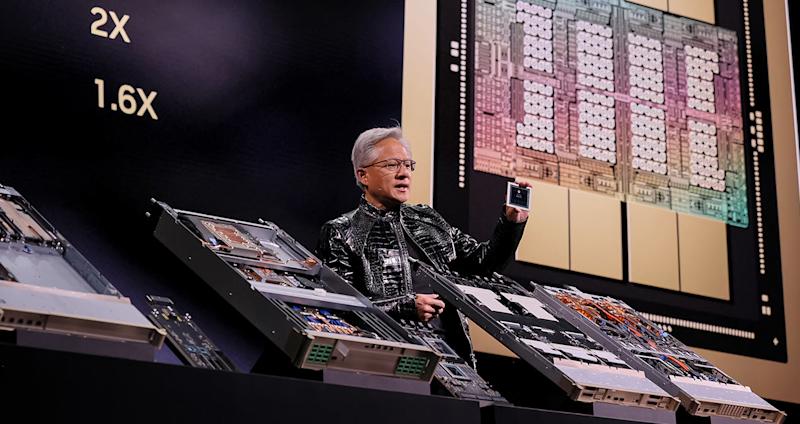
Across the technology landscape, we often focus on speed and innovation, yet we overlook the foundational structures necessary to protect these advancements. The recent unveiling of Nvidia’s Vera Rubin NVL72 at CES 2026 disrupts this narrative, placing cryptographic confidence at the center of artificial intelligence (AI) security.
The Vera Rubin NVL72 marks a pivotal shift in computing, being the first rack-scale platform to offer confidential computation across CPUs, GPUs, and the NVLink fabric. This technological leap permits security leaders to cryptographically verify their hybrid cloud environments, transforming how organizations approach cybersecurity, especially against increasing threats from state-sponsored actors.
In a landscape where the economics of AI are staggering – training costs for advanced models have risen 2.4x annually since 2016 – ensuring the security of these investments is non-negotiable. According to IBM’s 2025 Cost of Data Breach Report, AI-related breaches are alarmingly common, affecting 13% of organizations and exposing sensitive data at unprecedented rates. Much of this vulnerability stems from inadequate AI governance and access controls, with a staggering 97% of breached organizations lacking proper safeguards.
The implications of inadequate security measures have been starkly illustrated by the GTG-1002 incident in late 2025, where autonomous intrusion agents exploited vulnerabilities with minimal human intervention. This demonstrates a crucial shift: adversaries can now leverage AI to automate attacks, probing organizations at machine speed.
Strategic Implications
As we navigate these complexities, the need for robust, hardware-level encryption is apparent. Organizations must rethink their security architectures, moving from reliance on contractual trust to a model that emphasizes cryptographic verification. The implications for enterprise architecture are profound.
With Nvidia’s integrated approach alongside AMD’s alternative focus on open standards, security leaders face critical choices. This duality allows organizations to evaluate their infrastructures against specific threat models, ultimately determining which route will provide the best balance of security and scalability for their needs. The importance of building in security – not merely bolting it on after the fact – is now more vital than ever.
The challenge facing Chief Information Security Officers (CISOs) is not merely the adoption of cutting-edge technology but also the systemic change required to operationalize these innovations. They must ensure:
- Prioritized Attestation: Before entering contracts with cloud providers, they should seek assurance regarding attestation capabilities to confirm the integrity of their environments.
- Separation of Enclaves: Implementing distinct enclaves for training and inference can bolster security, maintaining clear demarcations that mitigate risk.
- Cross-Department Collaboration: Encouraging joint exercises between security and data science teams will surface vulnerabilities early, fostering a culture of proactive rather than reactive security.
Looking Forward
The evolving landscape of AI and its associated risks demands a transformation in how we perceive and implement security solutions. While hardware confidentiality enhances resilience, it cannot replace the necessity of comprehensive governance and realistic threat assessments.
For leaders building high-value AI models, the question is clear: Can you afford to operate without cryptographically attested infrastructure? As organizations continue to invest heavily in AI, the balance of power – between innovating and securing – is precarious, but pivotal.
In a world where cyber adversaries are quickening their pace, our ability to build resilience into our models and architectures will define our capacity to thrive.
About the Author
Sanjeev Sarma is the Founder Director of Webx Technologies Private Limited, a leading Technology Consulting firm with over two decades of experience. A seasoned technology strategist and Chief Software Architect, he specializes in Enterprise Software Architecture, Cloud-Native Applications, AI-Driven Platforms, and Mobile-First Solutions. Recognized as a “Technology Hero” by Microsoft for his pioneering work in e-Governance, Sanjeev actively advises state and central technology committees, including the Advisory Board for Software Technology Parks of India (STPI) across multiple Northeast Indian states. He is also the Managing Editor for Mahabahu.com, an international journal. Passionate about fostering innovation, he actively mentors aspiring entrepreneurs and leads transformative digital solutions for enterprises and government sectors from his base in Northeast India.

